Phishing is an ever-evolving type of fraud that can occur both online and offline, and can result in scammers gaining access to your personal information, such as your email address, passwords, and even your credit card details.
To help ensure your private information stays private, in this article I’m going to give you the tools you need to spot phishing emails, popups and instant messages, as well as offline phishing scams such as fraudulent SMS and phone calls.
By the end of this article, you’ll have sharpened your scam-spotting skills, so the next time a phishing email arrives in your inbox, you won’t be tricked into handing over any personal information.
Never trust random popups
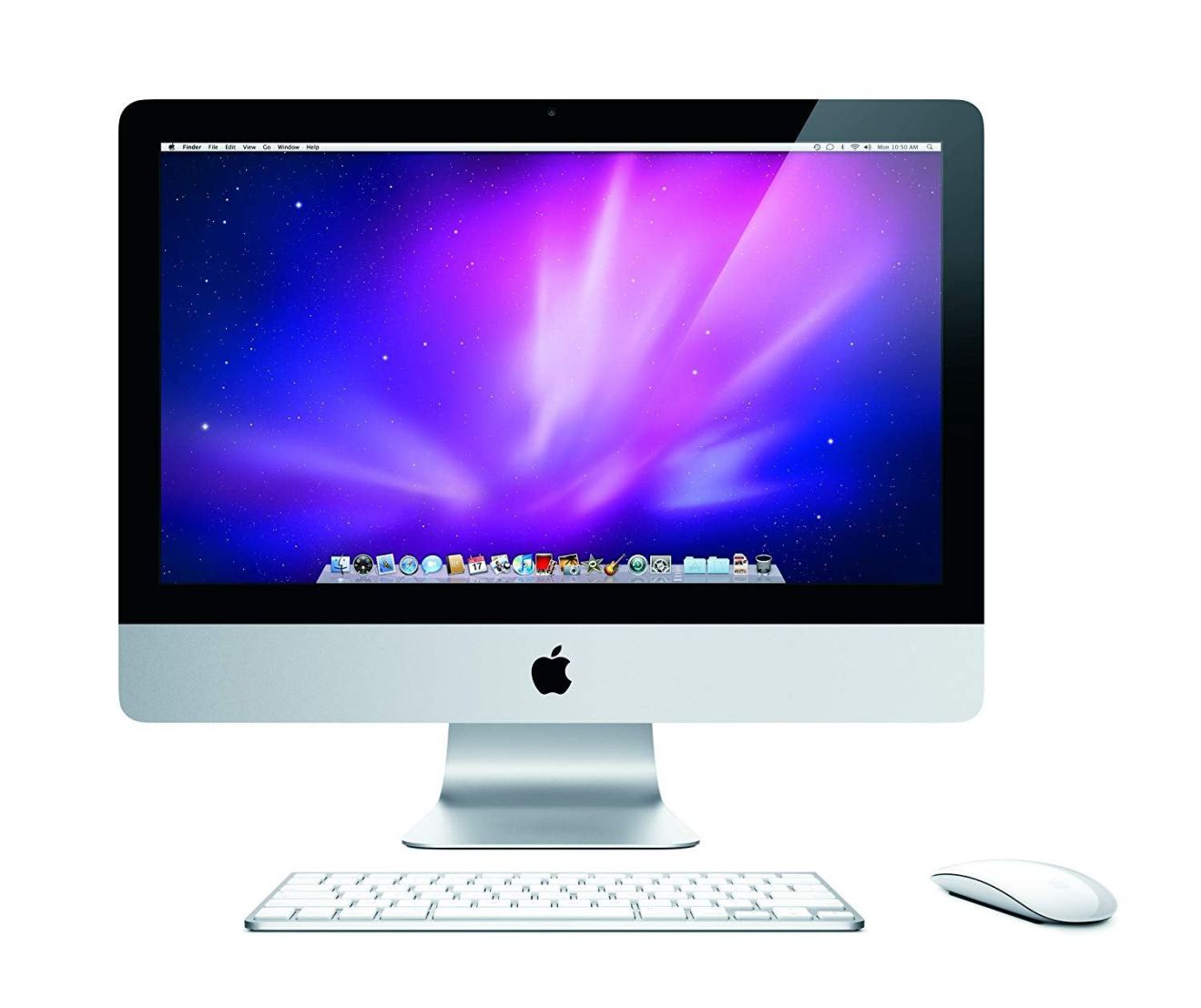
Have you ever been browsing the web, when a window, tab, popup or instant message has appeared onscreen, claiming that your Mac is infected with malware? Typically, these windows promise to remove the malware or virus – and all you have to do is follow a link, download a program, call a number, or perhaps hand over some personal information such as your email address or credit card details.
While these warnings can be effective at striking fear into the hearts of Mac users, they’re almost guaranteed to be a scam.
Keeping your Mac malware-free requires you to be vigilant and proactive – if only it was as simple as following the instructions in some random popup! In reality, malware is such a huge and complicated threat that there are entire industries dedicated to helping consumers keep their computers malware-free. Today, there’s countless software companies that specialise in anti-malware programs; cyber security consultants, and websites dedicated to sharing tips, tricks and news on how to protect yourself against the latest Mac malware.
If you do ever encounter this kind of unsolicited warning, then you should close the window, popup or tab in question, and navigate away from the website that triggered this warning. Most importantly, never act on these popups, regardless of whether they’re asking you to download a piece of anti-virus software, perform a scan, or even call a number for some free, “professional” advice.
And, if a popup does leave you paranoid that your Mac may be infected, you can always scan for potential malware, or use one of the many legitimate programs that are designed to identify malware and other digital threats, such as the Knock Knock app.

Become a pro at spotting phishing scams
There’s many ways that scammers can get hold of your email address, ranging from data leaks and breaches, to brute force attacks, or even simply guessing your email address.
Once a scammer has your address, they can trick you into handing over personal information by impersonating other companies, and some of these email scams are notoriously difficult to spot.
Imagine you receive an email claiming to be from Apple, warning that suspicious activity has been detected in your iCloud account, and advising you to change your password immediately. This email has the correct header, footer, formatting, and uses the language you’ve come to expect from Apple’s password reset emails, and it links you through to a password reset page that, at first glance, seems completely authentic. Rattled at the thought of someone gaining access to your iCloud account, you do exactly what the webpage asks: you enter your username, your old password, and the new password that you want to use. Job done! Now you can sit back, confident that whoever was trying to access your account is now locked out forever.
Except that this was all a scam, and you’ve just handed the scammer all the information they need to hack into your iCloud account.
If a scammer puts enough effort into crafting an email and a webpage that look like the real deal, then these scams can fool even the most tech-savvy of Mac users.
If an email ever rouses your suspicions, then you can check its authenticity by reaching out to the company or organisation directly, via a channel that you know to be authentic. In our iCloud example, you could head over to Apple’s official Contact Us page, and ask them to take a look at the email you’re concerned about – after all, it’s in their interest to identify any scammers who might be trying to hack into their services!

Since there’s always a chance that a suspicious email might turn out to be genuine, in this scenario you should also change your iCloud password, just in case there really is suspicious activity in your account. However, play it safe and don’t reset your password via any of the links in the suspicious email – head over to the iCloud site and follow the links to a password reset page that you know to be genuine.
While this type of email scam can often be difficult to spot, there are some telltale signs that can help you distinguish the legitimate emails, from the not-so-legitimate emails.
- Is the message unsolicited? Not all unsolicited emails are scams, but a message that’s sent in direct response to one of your emails is always going to be more trustworthy than one that appears in your inbox at random, especially if it’s from an email address that you don’t recognise! It’s a good idea to be just that little bit more critical of unsolicited emails, particularly if the message is asking you to perform an action, such as click a link; requesting personal information, or if the email contains an attachment.
- Is the greeting oddly vague? If an organisation has access to your name, then you can generally expect them to use it! If the email is supposedly from an organisation you’re familiar with, but it starts with a generic greeting such as “To our valued customer,” or “Dear sir,” then this should ring some alarm bells!
![]()
- Check the contact details. It’s pretty common for email footers to contain a wealth of contact information, particularly emails that are sent by an organisation or business. If the email contains any contact details, then try running them through a search engine, to see whether they really are associated with the organisation in question. If the phone number, email address or website doesn’t seem to be linked to the correct organisation, then this is a huge red flag. However, note that just because an email contains the correct contact details, doesn’t guarantee that this email is legitimate – after all, anyone can copy/paste official information into an unofficial email!
- Check any URLs, without clicking them. If an email contains a URL, then most of the time it’ll be presented as an embedded link, rather than visible text. For example, you’re far more likely to encounter a ‘Change your password now’ button containing an embedded link, rather than a visible www.mywebsite/change-your-password URL. However, just because a URL isn’t immediately visible, doesn’t mean you can’t check where it leads! Most browsers and email providers let you preview embedded links by hovering over them, at which point the URL will be displayed somewhere onscreen, for example as a tooltip or in the corner of the browser window. Once you know where the email is trying to take you, you can check whether it correlates to any of the organisation’s official webpages. For example, you should be very suspicious of a iCloud password reset email that’s pointing you anywhere other than the official iCloud.com domain.
- Does the email just sound “off?” Sometimes, it can be difficult to put your finger on what’s making you so suspicious. If you’ve received any previous emails from this person or organisation, then it can help to compare the new email with the old one, to see whether there’s any noticeable differences in the layout, language, or tone. This comparison can help you zero in on why this email isn’t sitting quite right with you.
- Does the email request personal information? No-one should ever ask you to share sensitive information over email. Even if everything else seems legitimate, if the email is requesting information such as your password or credit card details, then this is a huge red flag.
Don’t get drawn into suspicious text messages, voicemails or phone calls
It’s far easier to ignore an unsolicited email or popup, than it is to hang up on a ‘real’ person, but sometimes that may be your only option!
If you receive a suspicious SMS or voicemail, then these are relatively easy to ignore, and for extra security you can always blacklist or block the phone number in question. However, if a scammer does manage to get you on the phone, then chances are they’ll use every psychological technique to try and manipulate you into doing what they want – ranging from bamboozling you with technical gibberish, to flattery, and possibly even threats.
If you suspect the caller isn’t who they claim to be, then never act on their advice or instructions, and remember that you can always hang up, if things get too uncomfortable.
If you’re unsure whether a caller is genuine, then you can always end the call and cross-reference their details with the company or organisation they’re claiming to represent. Sometimes, this may mean getting the company’s phone number from their website and checking whether they have any record of the call; or it may mean putting the caller’s number into Google to see whether it returns any results, as there’s plenty of websites and forums where people share details about the nuisance and scam calls they’ve received.
Specifically, if you receive an unsolicited phone call, voicemail or SMS from anyone claiming to be from Apple, then Apple advise you to report this to them directly.
Before you go
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.




Add Comment