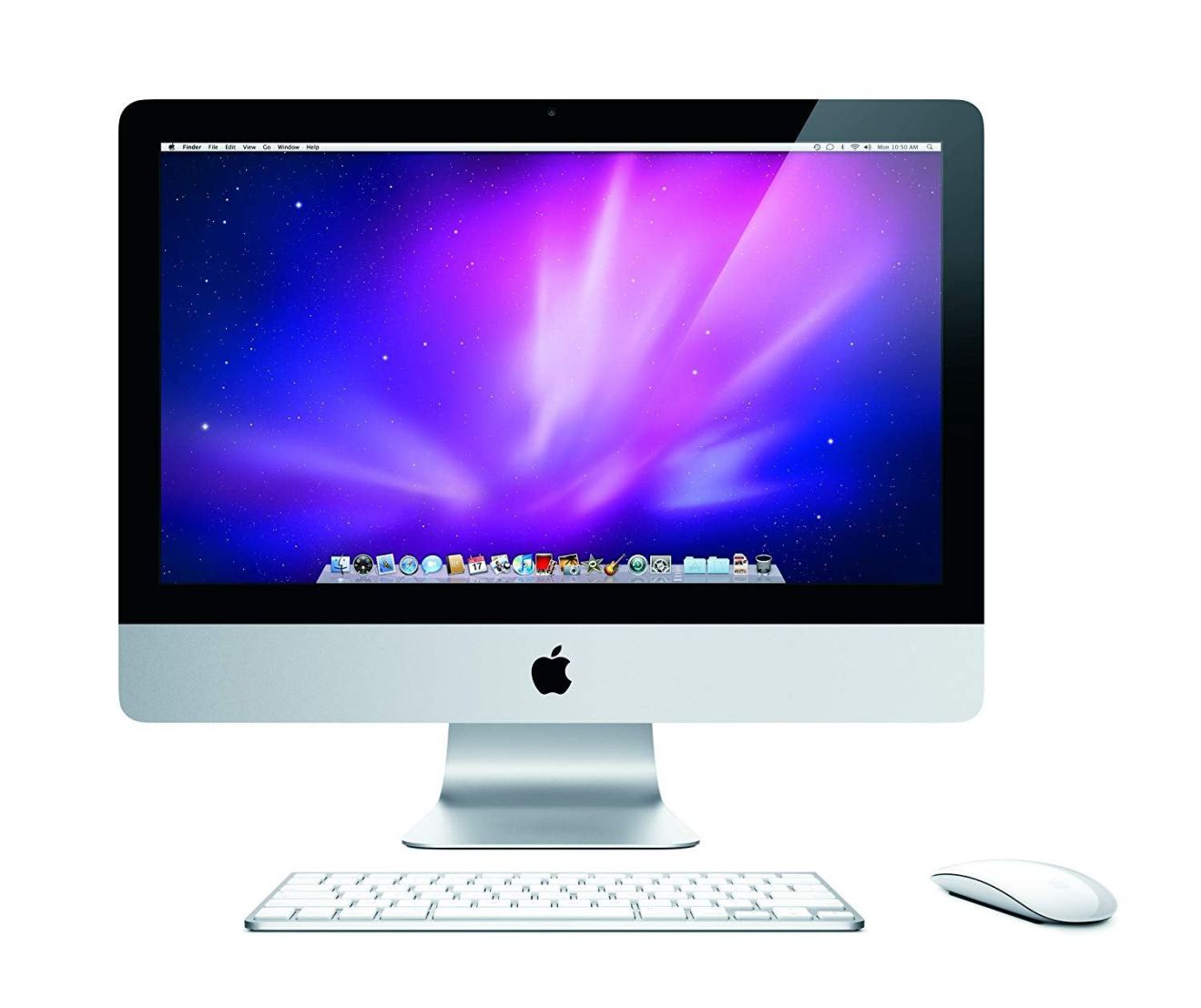
In this article, we’re going to look at one particular kind of -ware that recently found its way onto Macs for the very first time. We’ll look at what it is, how it works, and the steps you can take to help keep your Mac safe.
This is everything you need to know about ransomware.
What is Ransomware?
Ransomware is a type of malicious software that is typically spread via a Trojan that contains a payload disguised as a legitimate file. Once installed on your computer, the ransomware starts encrypting your files, preventing you from accessing them. The hacker then demands a ransom in return for decrypting your files.
So as a Mac user, just how worried should you be about ransomware?
In March 2016, you may have seen reports about “KeRanger,” which is believed to be the first time fully-functioning ransomware that found its way onto Macs.
KeRanger was spread via an infected version of Transmission, an open source BitTorrent client. This particular version had been modified by a third party to include a General.rtf file, which turned out to be a malicious executable file masquerading as a rich-text document.
After sitting quietly on the user’s system for three days, KeRanger would suddenly start encrypting the victim’s files, leaving behind multiple “README_FOR_DECRYPT.txt” files containing details about how the malware’s author would hand over a decryption key in return for one bitcoin (roughly $400).
Macs are well-known for having numerous built-in security features, but KeRanger managed to slip through MacOS’ defences as it was signed with a valid Mac developer certificate. Once KeRanger was identified as ransomware, Apple revoked the abused certificate and updated MacOS’ XProtect mechanism to block this particular version of Transmission.
While it’s comforting to know that Apple sprung into action as soon as the threat was discovered, Apple can only block malware that it knows about. And realistically, Apple are probably only going to discover a new threat after it’s started affecting Mac users.
Mac ransomware is still pretty rare, which means it currently only poses a slight risk, however if you are unlucky enough to be affected by malware the consequences are serious. No-one wants to permanently lose access to their most important files!
So what steps can you take to limit the chances of getting locked out of your own Mac?
Consider downloading some extra protection
While Macs do feature some built-in security features, there’s no such thing as too much security, so you may want to download software that’s designed to guard against ransomware specifically. One tool you may want to try is RansomWhere?
Rather than protecting you against specific ransomware threats, RansomWhere? monitors your file system for any untrusted processes that suddenly start creating encrypted files, which is a tell-sign of ransomware activity.
If RansomWhere? detects this kind of rapid encryption, it suspends the process responsible and presents the user with a dialogue containing the name of the process and a list of all the encrypted files it’s created. The user can then choose to terminate the process or, if the process has a legitimate reason for creating so many encrypted files, they can allow the process to continue running.
This tool does have a few limitations that you need to be aware of. Firstly, RansomWhere? can only spot ransomware after it starts encrypting files, which means you will lose access to a few files. Also, when you install RansomWhere? it whitelists every app that’s already present on your Mac, and automatically trusts all apps that are signed by Apple, which means it can’t detect ransomware that abuses a signed Apple binary.
However, even with RansomWhere?’s limitations, it can still be a useful addition to your malware-fighting arsenal. If you want to try RansomWhere? for yourself, then you can download it for free.
Scan for ransomware
You may also want to download a tool that scans your Mac for malware.
One such program is Malwarebytes, which scans for code that impacts your Mac’s performance or attacks the system, and then removes this malicious code. Since Malwarebytes isn’t ransomware-specific, it can help protect you against the full range of malware threats.
Malwarebytes is available as a free download for personal use, although if you do opt for the free version you’ll have to launch the program manually everytime you want to perform a scan. If you purchase the paid version, then you can create a schedule where Malwarebytes scans your system automatically.
Once you’ve installed Malwarebytes, launch it and give the ‘Scan’ button a click.

By making a point to scan your Mac regularly, you increase your chances of catching ransomware before it has a chance to do too much damage.
Stay informed
The most effective way of avoiding ransomware, is to keep up to date on the latest Mac security threats.
Hopefully this knowledge means you never download any infected software, but even if it turns out that you have installed the latest ransomware, you may still be able to remove it from your computer before it does too much damage – remember that KeRanger sat on each victim’s Mac for three days before it began encrypting files. The secret is keeping up to date on Mac security threats, so you can act on this information as quickly as possible.
Find a couple of good Mac and Apple websites, blogs and social media accounts, and keep an eye out for any malware-related news. You may also want to set up Google Alerts so you receive automatic notifications whenever news sites post stories featuring certain keywords, for example you could create Google Alerts for “Mac” and “ransomware,” or “Apple malware.”
Act on XProtect warnings
Every Mac comes with a whole host of security features that can help keep you safe from ransomware – but only if you pay attention to them!
One particularly effective MacOS security feature is XProtect, which maintains a list of known malware that gets updated as new threats are discovered. Everytime you download a file and attempt to launch it for the first time, XProtect checks its list of known malicious software, and notifies you if it finds a match.
You should always read any messages that appear when you try to launch an app for the first time. If the popup warns you that this app will damage your computer, then immediately move this app to the Trash and empty your Trash folder.
If you see a warning that: “X application can’t be opened. You should eject the disk image,” give the ‘Eject disk image’ button a click and follow the onscreen instructions. Then once again you should drag this app to the Trash and immediately empty the Trash.
The next step is to delete any files that are associated with this app, for example if the app arrived via a separate installer then you should delete this too.
You also need to be aware that simply deleting an app and any obvious associated files may not be enough to remove the ransomware completely. It’s possible for malware to generate additional files and stash them away in other parts of your file system, or it may launch a malicious process, so you’ll need to do a bit of research to check whether this is the case.
When malware is discovered, technical specialists are typically quick to name all the files and processes that are associated with this malware, so do a bit of online research to see whether there’s any other files or processes you need to remove.
You can identify and delete files using the ‘Finder,’ and you can terminate processes by launching the Activity Monitor app (Applications/Utilities/Activity Monitor), selecting the process in question and giving Activity Monitor’s ‘Force quit’ icon a click (where the cursor is positioned in the screenshot below).

The major drawback is that XProtect can only warn you about known malware. If you’re curious to see exactly what malware Apple is protecting you against, you can read XProtect’s list of blacklisted software by opening your Mac’s ‘Finder’ and navigating to /System/Library/CoreServices. Control-click the XProtect.bundle file and select ‘Show Package Contents.

A new ‘Contents’ folder should appear. Navigate to Contents/Resources and open the XProtect.plist file to see complete list of all the programs that XProtect recognises as malware.

If you fall victim to ransomware
Hackers are coming up with new malware all the time, so even if you follow all the advice and keep up to date on the latest cyber threats, that’s still no guarantee that you won’t wind up on the receiving end of a ransomware note at some point.
Even in the worst case scenario where ransomware has already encrypted all your files, all is not lost! In this section I’m going to share several techniques that you can use to help recover encrypted files.
But first, an important message: whatever you do, don’t give in and pay the ransom.
While it may be tempting to give into a hacker’s demands in the hope of regaining access to your files, there’s a few reasons why this is always a bad idea.
Firstly, there’s no guarantee that the hacker will even send you the decryption key as promised. In fact, if the ransomware is badly written then it’s possible that the author may not even be able to unlock your files anyway. You may receive a decryption key that doesn’t work, or you may receive nothing at all.
It’s also possible that the hacker may decrypt your files, only to re-encrypt them at a later date in order to get more money out of you. From their perspective, if you were willing to pay up once, then you’re likely to pay a second time, too.
There’s also the issue of being a good member of the Apple community. Although Mac ransomware is currently pretty rare, the more Mac users who give into ransomware demands, the more ransomware we’re likely to see.
So do your fellow Mac users a favour and don’t give into ransomware – no matter how tempting it might be.
Try restoring a Time Machine backup
Depending on the particular strain of ransomware, you may be able to recover your files by restoring a Time Machine backup from a time before the ransomware infected your Mac.
To restore a backup, boot into Recovery mode by restarting your Mac and holding the ‘Command’ and ‘R’ keys until you see the Apple logo. Once you’re in Recovery mode, select ‘Reinstall from Time Machine Backup’ from the OS X Utilities window and follow the onscreen instructions to select and restore one of your backups.
Just note that some ransomware may attempt to encrypt your Time Machine backups. For example, when analysing KeRanger, researchers discovered a “_encrypt_timemachine” function that appeared to be complete, but hadn’t been activated.
If you’re unlucky enough to encounter ransomware that does encrypt your Time Machine backups, then unfortunately recovering your Mac won’t be as straightforward as restoring a backup, and you may need to reinstall your entire operating system.
Reinstall your operating system
This is a drastic measure, but if you’ve tried everything else and your Mac is still locked down tight, then this may be the only way to flush out the ransomware.
Reinstalling your operating system is effectively the same as performing a factory reset, so you’ll lose the entire contents of your Mac. Hopefully you saved all your most important files to the cloud, via a service such as iCloud, Google Docs or Photos, so you won’t lose everything.
To reinstall your operating system, boot into Recovery then select ‘Reinstall OS X’ and follow the onscreen instructions.
Before you go
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.



Add Comment