Being tracked by online advertisers is something we all worry about. There’s something seriously unsettling about searching for a product once, only for that exact same product to suddenly crop up in every single advert you encounter across the web!
According to Freedom to Tinker, advertisers have a discovered a new way to track your online movements, and are now tricking your password manager into leaking your personal information. This exploit is particularly worrying, as not only does it have the potential to expose your name, username and email address to third parties, but it could expose your passwords as well. Freedom to Tinker have discovered scripts that are actively using this password manager loophole on 1110 of the Alexa top 1 million sites.
At the time of writing, all third party password managers were vulnerable, including the password managers that are built into all the major web browsers. Even if you don’t use a third party password manager, as long as you use a web browser you need to be concerned about this exploit!
In this article, we’ll look at how advertisers are using this auto-fill loophole to track your online movements, and what you can do to protect yourself.
How is auto-fill leaking my information?
Passwords managers are designed to remember the name, username or email address, and password combo that you enter into a website. The next time you visit that website, the password manager will auto-fill these fields, resulting in a more seamless login experience, especially if you’re the kind of person who struggles to remember their login details!
Now, some third party advertisers are exploiting this auto-fill behaviour, by injecting fake, invisible boxes into web pages. As soon as the password manager detects these fields, it auto-fills them without notifying the user, and the third party script can then extract this information and send it back to the advertiser’s server. The third party can then use this information to track you with targeted adverts across the World Wide Web. Since the fake forms are invisible, you won’t even know that your password manager has just been tricked into handing over your personal information!
Email addresses are particularly useful for advertisers, as even if you regularly clear your browser history and cookies, or use private browsing mode, your email address is unlikely to change, so the third party will still be able to track you. Even moving to a new device might not be enough to shake off the advertiser, as you’ll typically take your old email address with you.
The third party tracking script doesn’t even need to be present on the screen where you initially create or enter your login details. As long as your password manager has this information, this script can run anywhere on the affected website. Note that the third party script must have access to the first party domain, so a script on the example.com domain can only extract your login details for example.com. A script on example.com cannot use this script to extract your Facebook or Gmail passwords, for example.
Freedom to Tinker have created a demo page where you can experience this script first-hand:
- Head over to the demo page.
- Enter a fake email address and password. This page is going to extract your information, so don’t use any real credentials!
- Click ‘Submit.’
- At this point, your default password manager will ask whether you want it to remember these credentials. If you don’t use a third party password manager, then this request will come from the browser itself, for example you’ll encounter a ‘Safari Password Preferences’ popup if you’re a Safari user, and a Google Smart Lock notification if you’re on Chrome. When prompted, save this information to your password manager.
- The subsequent page will run a third party script and display all the information it’s managed to extract via the auto-fill loophole – whether that’s your username, your password, or both.

In the worst case scenario, this script has just extracted your password and you use this same password across multiple accounts. The person behind the script now has access to all of these accounts, which might be anything from your social media profiles, to your work email, or even online shopping accounts where you’ve stored your credit card details!
Although there’s currently no evidence to suggest that these scripts are sniffing out people’s passwords, this demo page proves that it is possible, so now’s the time to act to make sure this worst case scenario doesn’t become a reality!
I use a third party password manager! What can I do to prevent auto-fill abuse?
This exploit relies on the password manager completing fields without asking your permission, so the easiest way to protect yourself is by disabling auto-fill.
With auto-fill disabled, every time the password manager encounters a field that it could potentially complete, it’ll display an icon alongside that field rather than completing it automatically. If you do want the password manager to complete this field, then you just need to give the icon a click. While this does add an extra step to the login process, it prevents the password manager from entering your personal information into suspicious, invisible fields.
Most third party password managers give you the option to disable auto-fill. The steps vary between password managers, so check your manager’s documentation for more details.
While it’s always disconcerting to discover that an app you trusted with your personal information is susceptible to malicious scripts, you shouldn’t see this as a reason to abandon your password manager.
Password managers aren’t just about convenience, they also make it easier to manage a large number of different, complex passwords. Having a unique password for every account ensures that even if someone does manage to get ahold of your password, they won’t immediately have access to all your accounts.
Even though this exploit is worrying, saying goodbye to your password manager could end up hurting your digital security in the long run, as you’ll be far more tempted to re-use passwords.
I use my web browser’s built-in password manager!
Most web browsers have a built-in password manager, so even if you don’t use a third party manager, you’re still susceptible to this exploit. In this section, I’ll show you how to disable auto-fill functionality for most of the major web browsers. I’ll also suggest a workaround that you can use, just in case your favourite web browser doesn’t give you the option to disable auto-fill.
Safari
To disable Safari’s auto-fill functionality:
- Select ‘Safari > Preferences…’ from the Safari toolbar.
- Select the ‘Autofill’ tab.
- Deselect the ‘User names and passwords’ checkbox.

Mozilla Firefox
If you’re a Firefox user, then you can disable auto-fill in the about:config menu:
- Type ‘about:config’ into the Firefox address bar, and then press the ‘Enter’ key on your keyboard.
- Search for ‘signon.autofillForms.’
- If ‘signon.autofillForms’ is set to ‘true,’ then Control-click it and select ‘Toggle’ from the context menu. This should switch it from ‘true,’ to ‘false,’ at which point auto-fill is disabled.

Chrome and Microsoft Edge
Currently, you cannot disable auto-fill for every single web browser. At the time of writing it wasn’t possible to disable auto-fill in Microsoft Edge, and Chrome only has options for disabling auto-fill in address and credit card fields, and not password fields.
It may sound counter productive, but if you can’t disable auto-fill in your favourite web browser, then you should switch to a dedicated password manager, and then disable auto-fill within this third party app.
What else can I do, to protect my online privacy?
This script is just the latest trick that third parties are using to track your online movements, so it’s recommended that you take additional measures to ensure your browsing sessions remain private. Here’s just a few extra ideas:
- Review your cookie settings. By default, Safari only accepts cookies from websites that you explicitly visit, but you can change these settings to block more cookies, or even prevent cookies from being placed on your Mac entirely. For more information, check out our guide to blocking and deleting cookies in macOS Sierra.
- Make a Do Not Track request. Many web browsers have a Do Not Track feature that sends a request to every website you visit, letting them know you don’t want to be tracked. Unfortunately, it’s up to individual websites to honour this request, so there’s no guarantee that every website you visit will act on your Do Not Track settings, but it’s still worth enabling. You can activate Do Not Enable in Safari, by selecting ‘Safari > Preferences…’ from the Safari toolbar, and then selecting the ‘Privacy’ button, followed by ‘Ask websites not to track me.’
- Regularly clear your history. Although this won’t necessarily prevent third party tracking, the less information that’s stored in your browser, the less information these third parties will have to work with. You can clear Safari’s cache and history, by selecting ‘History > Clear History’ from the Safari toolbar.
- Use Private Browsing. Again, this won’t necessarily prevent third party tracking, but it will limit how much information they have access to. Whenever you close a Private Browsing window, Safari will automatically discard all the data associated with that session, including cookies, history, cache, auto-fill information, and website data. To start a Private Browsing session, select ‘File > New Private Window’ from the Safari toolbar.
- Use an ad blocker. There’s evidence to suggest that ad blockers might be able to prevent tracking, by blocking the domains that are used to deliver invasive third-party scripts. For more info, check out our guide to ensuring you never see another online ad again.
- Keep track of third party trackers! This security exploit has highlighted the fact that we never really know who’s watching our online movements. Disconnect Private Browsing is a browser extension that aims to shed some light on the third parties, advertisers, and other organisations who might be trying to track your browsing sessions, by notifying you whenever Safari receives a tracking request. This extension also lets you see exactly where each of these tracking requests originates from.
- Switch to the Tor browser. This browser may have a reputation of being associated with the Dark Web, but the reality is much less scary: Tor is a modified version of Firefox and a network that disguises your identity using a technique known as “onion routing.” Whenever you visit a website using the Tor browser, your Internet traffic gets bounced around numerous randomly-selected nodes, before exiting the Tor network and arriving at the server. This technique does result in Tor being noticeably slower than many other web browsers, but it’s also pretty effective at concealing your identity from anyone who might be trying to spy on you. Want to start using Tor? Check our our complete guide to browsing the web anonymously.
Before you go
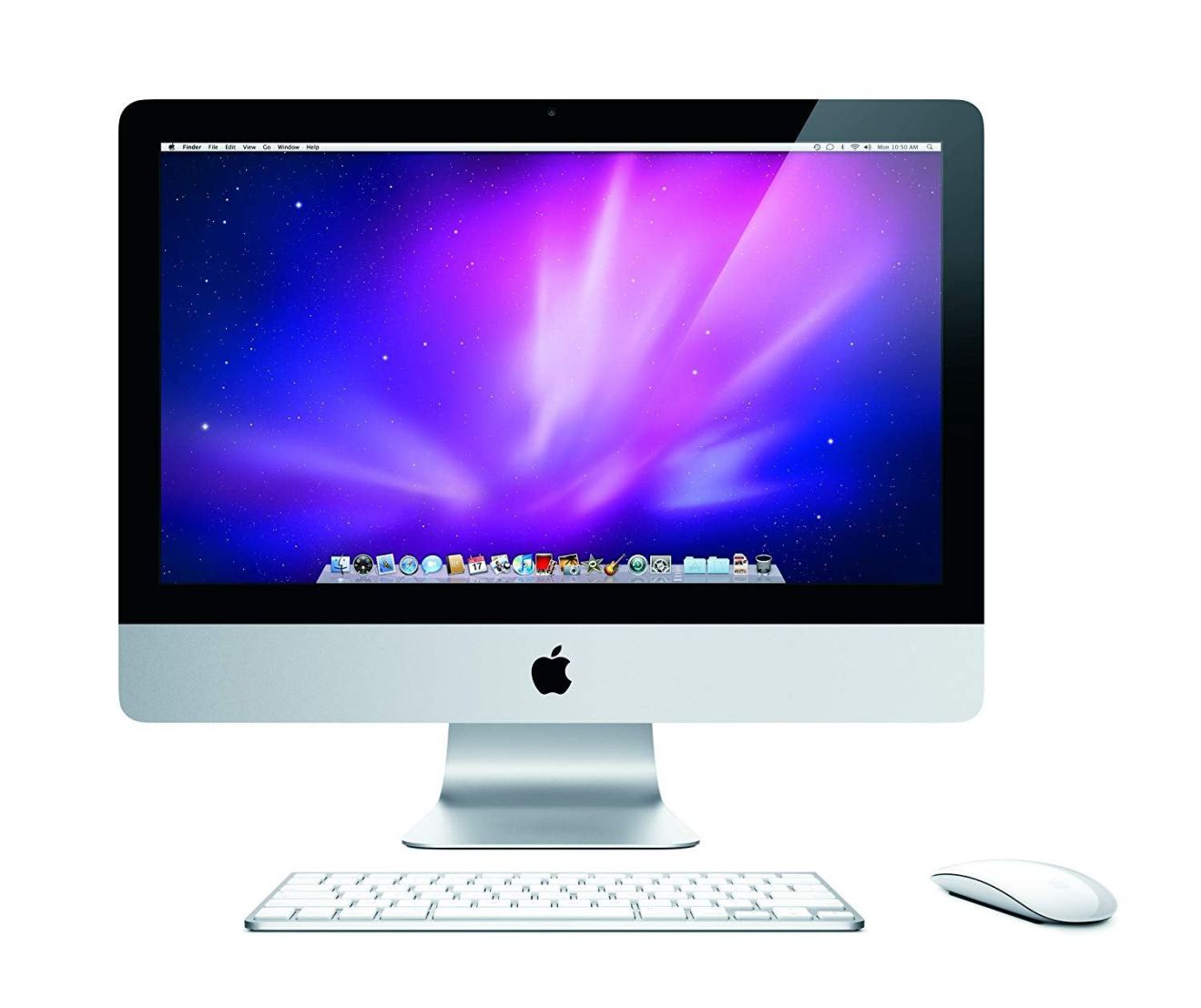
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.



Add Comment