Grant Thompson, a 14-year-old American teenager who recently revealed a security bug in Apple’s FaceTime, will receive a “bug bounty” from the firm, as well as a grant to further his education. The precise amount is unknown but, in similar cases in the past, Apple has forked out roughly between $25,000 and $200,000.
This is not easy money though – the firm only pays “bounties” for five different classes of exploits, and the programme is presently only available by invitation.
This is why Apple is now being held to ransom by a German teenager who discovered a critical bug in macOS that enables hackers to access private information from the Keychain without admin privileges.
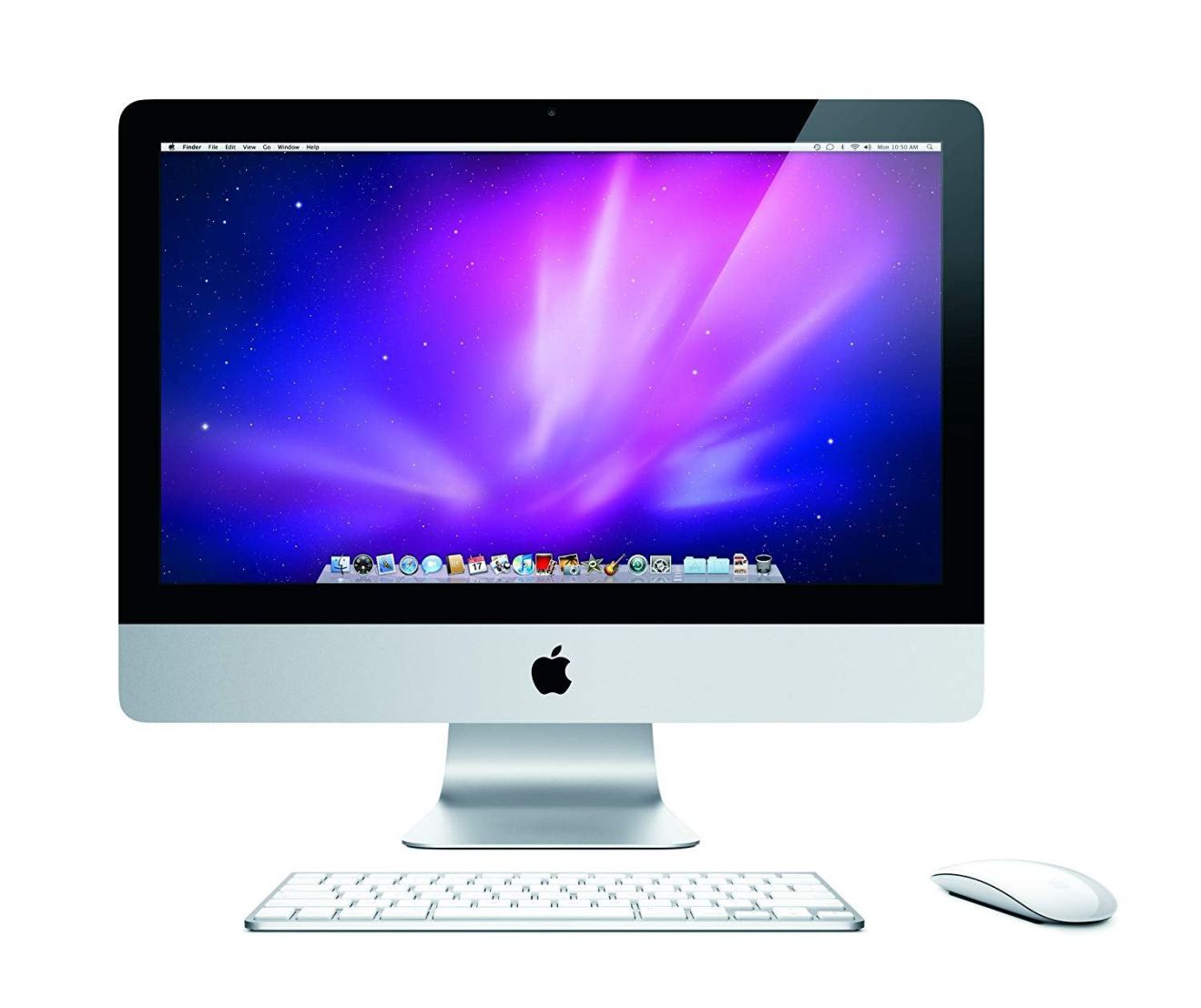
Keychain Access stores users’ passwords so that they don’t have to remember them every time they visit a network server, email account or website. This means that the bug might give access to banking, Facebook and Netflix login information, among others.
18-year-old Linus Henze recently uploaded a YouTube video in which he revealed exactly how easy it is to get a user’s login credentials from their Apple computer. In the video description, he states: “In this video, I’ll show you a zero-day exploit that allows me to extract all your (local) keychain passwords on macOS Mojave, and lower versions.”
Henze won’t reveal any details about the exploit until Apple adds MacOS exploits to its bug bounty programme, which currently only applies to iCloud and iOS vulnerabilities.
He added that he actually loves Apple products but that he would like them to be more secure – and a bug bounty programme similar to what other firms already have would be the best way to achieve this.
He was probably referring to Google and Facebook, which have paid out around $14.91m and $7.455m respectively since launching their bug bounty programmes.
Before you go
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.



Add Comment