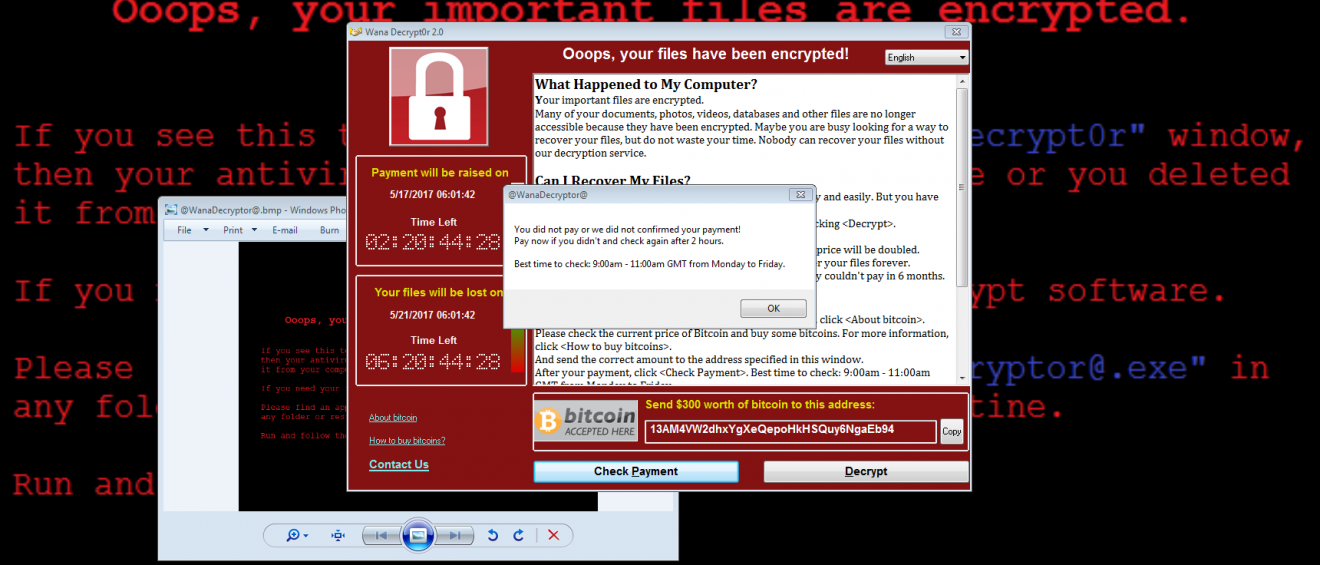
Mac users beware: the latest malware variants specifically target Apple computers. One variant of the ransomware encrypts files and then demands payment to restore everything to normal. There is also spyware that monitors users’ actions in search of valuable data.
According to experts, both represented a threat.
The malware was discovered by security experts AlienVault and Fortinet, which uncovered a portal on the ‘dark web’ Tor network which served as a shopfront for both of them.
Fortinet said in a blog that the creators of the spyware claimed on the website that they were professionals with vast experience of writing working code. Prospective users were asked to explain to them how they preferred the malicious software to be set up because payments made by victims would be shared between the programmers and those who implemented their software.
Fortinet researchers subsequently pretended that they wanted to use the malware scripts and were duly sent examples of the code. Upon analysing the structure, they found it didn’t use the highly refined encryption techniques used in similar Windows variants.
However, this also meant that decrypting infected files was problematic, actually increasing the risk of lost data.
The researchers stated: “Even if it is far inferior to most current ransomware targeting Windows, it doesn’t fail to encrypt victim’s files or prevent access to important files, thereby causing real damage.”
The MacSpy spyware, freely downloadable from the same site, can take screenshots, record what is typed and tap into the microphone of the targeted device.
Peter Ewane, a researcher at AlienVault, said the spyware was designed to sidestep processes normally used by security programs to expose and eliminate them.
Fortinet’s Aamir Lakhani said: “Mac ransomware is definitely becoming bigger. Although market share is still small, hackers know that there is valuable data on the Mac.”
Apple has not offered comment on the latest developments in relation to security issues.
Before you go
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.



Add Comment