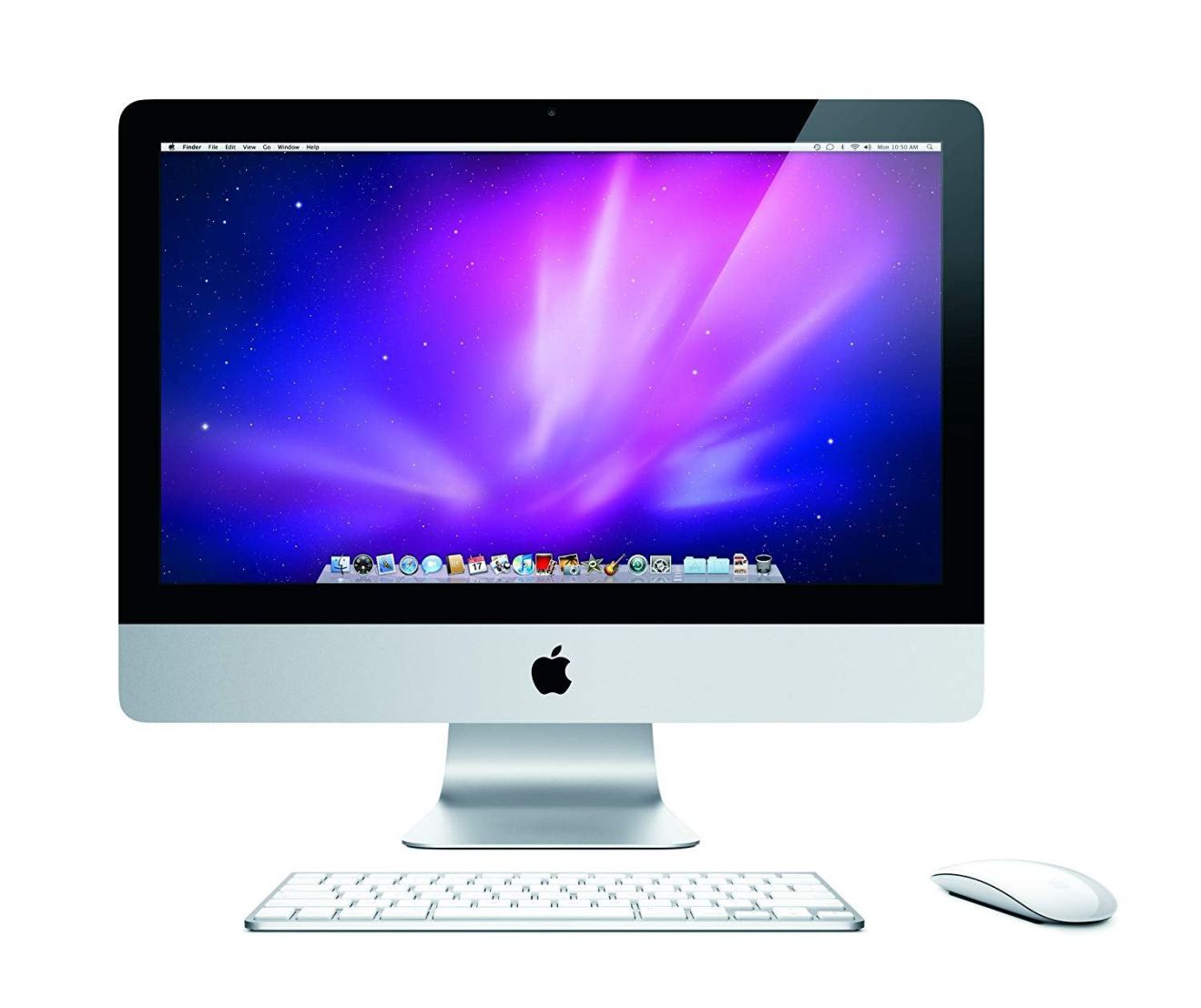
It’s not every day we hear about a malware attack targeting Apple Macs, but law enforcement agencies are investigating reports about a particularly dangerous piece of malware that has recently been attacking Macs with the sole aim of spying on users.
Ex-NSA agent Patrick Wardle, presently employed by cybersecurity company Synack, said he personally knows about nearly 400 attacks, but there were probably more. He added: “I likely only saw a limited percentage of the total number of victims.”
Wardle was able to trace Fruitfly victims via a backup domain the attackers used when their main servers went offline.
He told Forbes that about 90% of the IP addresses targeted were in the US. He handed his findings to law enforcement agencies and will be talking about the issue at this week’s Black Hat conference.
Wardle is convinced the primary aim of the cyberattack is surveillance, because the malware can spy on people’s webcams and also take screenshots. There are no keyloggers, no ads, and no ransomware — but there is a feature which alerts the person on the other side of the screen when the user becomes active.
The spyware uses outdated references to Mac OS X Yosemite updates, indicating it is at least three years old. At present, it is not clear precisely how the spyware was able to infect victims’ computers.
According to Malwarebytes, Fruitfly also attacked biomedical research firms earlier this year. The company says the attacks were highly targeted and difficult to trace. Thomas Reed, a researcher for the company, wrote earlier this year: “Although there is no evidence at this point linking this malware to a specific group, the fact that it’s been seen specifically at biomedical research institutions certainly seems like it could be the result of exactly that kind of espionage.”
Apple is yet to respond to the news.
Before you go
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.




Add Comment