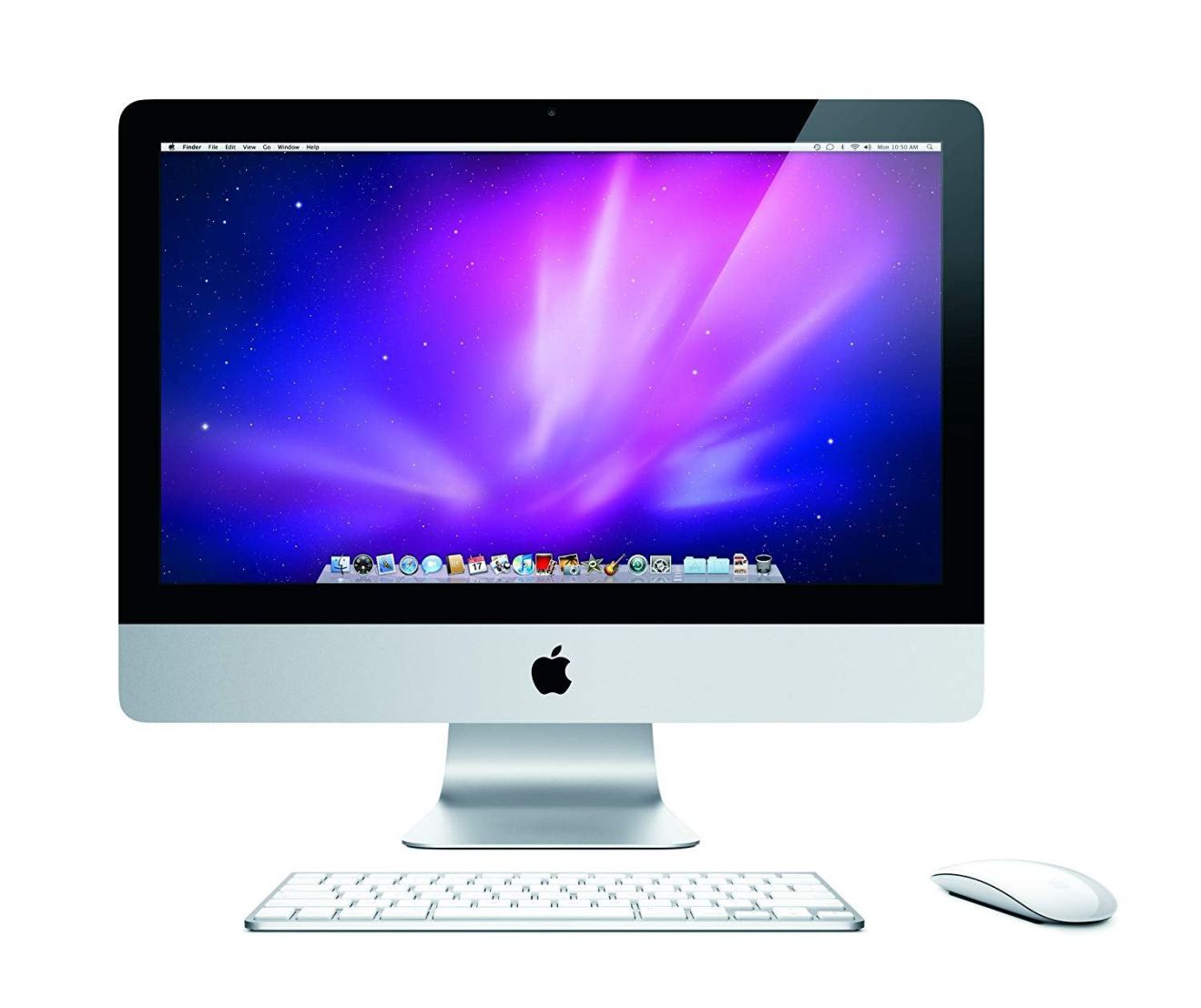
Researchers have discovered another password bug that affects Apple’s Mac operating system. This is the third similar discovery in the past few months.
The vulnerability enables anyone to modify someone’s preferences in the company’s AppStore by simply entering a fictitious password. It was revealed by Open Radar, a site for Apple developers.
Any user who could access the computer would be able to switch off app updates, security updates or macOS updates. The glitch is activated by simply hitting the unlock padlock when asked to enter system preferences and then typing anything you want as a password.
This reportedly affects Macs running on older operating systems, before MacOS 10.13, and only relates to preferences for the AppStore.
The latest embarrassment, which reared its ugly head on Wednesday, caused quite a bit of alarm among the security crowd – although experts pointed out that the bug was only a problem if someone else could physically access your Mac.
Four months ago, a researcher revealed how to download passwords by abusing Apple’s Keychain tech. And two months ago, another user discovered that anybody could access a Mac computer by simply entering ‘root’ as the password.
Apple fixed the problem in days, but the PR damage was already done.
Apple, Amazon, Google and Microsoft are presently working on solutions for the Spectre and Meltdown vulnerabilities that can be found in their hardware. These bugs are present in ARM, AMD and Intel microprocessors used by billions of devices, including Macs, iPhones, iPads, PCs and smartphones.
It might enable hackers to gain remote access to every single file stored on your device, including passwords, encryption keys and browsing history.
Intel’s CEO, Brian Krzanich, said earlier this week that they would issue patches for 90% of all devices that were affected by the Spectre and Meltdown bugs within the next two weeks.
Before you go
After spending over 20 years working with Macs, both old and new, theres a tool I think would be useful to every Mac owner who is experiencing performance issues.
CleanMyMac is highest rated all-round cleaning app for the Mac, it can quickly diagnose and solve a whole plethora of common (but sometimes tedious to fix) issues at the click of a button. It also just happens to resolve many of the issues covered in the speed up section of this site, so Download CleanMyMac to get your Mac back up to speed today.




Add Comment